When visiting a web resource, a person usually leaves a lot of information about himself. And without due measures on the part of the site owner, these personal data may be stolen. If you don't want something of the sort to happen, think about using SSL technology. Believe us, the intention to purchase an SSL certificate would be a good decision able to strengthen your business. In the end, Stolen data leads to your loss of reputation, and you obviously don't need it, right? That’s why it’s essential to be aware of mobile application security challenges.
But what are SSL certificates and how do they work? Let’s see!
What is an SSL connection?
First of all, what does SSL mean?
In essence, SSL stands for Secure Socket Layer; that is, as you see, even the name indicates we’re talking about the protection of user information. But, probably, we should be more specific! Okay, what is a Secure Socket Layer - globally?
SSL is a data transfer security protocol. And in the web hosting industry, the SSL term is often used as a synonym for HTTPS, which isn't entirely correct. In fact, the difference between SSL and HTTPS is rather significant.
The HTTPS protocol means a secure connection established between the user's web browser and the server hosting the website. In other words, HTTPS is SSL, which runs over HTTP.
So, SSL and HTTPS concepts are really interrelated, that’s true, though, HTTPS SSL is by no means the only option. SSL is quite versatile and can also work over other application layer protocols besides HTTP.
Who needs SSL authentication?
Of course, an SSL website is a good choice anyway, even if we're talking about a simple online resource. And yet, the main target audience of SSL providers is the websites of banks, payment systems, corporations, e-commerce platforms, social networks, state enterprises… in other words, technology is required by companies conducting payment transactions or actively using the personal data of their customers. In such a case, an SSL secure connection is a must-have condition.
However, today SSL protection has almost become one of the rules of good form and therefore it's being used everywhere — especially in industries like encrypting personal data in travel apps.
Is it possible to hack SSL websites?
Alas, hacking an SSL website is as easy as doing so with a regular resource. The benefit of secure socket layer technology is quite different.
The fact is that if you figure out how to create an SSL certificate and start using this technology, your users' personal information will remain safe.
Simply stated, the SSL security system protects the information exchanged with the user from being intercepted. In addition, these certificates confirm you're dealing with an authorized web resource, which belongs to a specific trusted owner. And you can be sure this isn't a phishing page or a clone site.
But let's discuss the purpose of SSL certificates more specifically, with examples, so you fully understand the basic idea.
What is SSL Protocol for?
Imagine the situation: you're making an online order and must enter your bank card number. The browser sends your private information to the server where a special program verifies the authenticity of your card and issues a purchase receipt. Then the bank withdraws money from your account.
Usually, the browser transmits all the information in the clear, so that the possible fraudsters, being on the transfer path, are able to intercept your data to use it as they wish to. You're likely to notice your card number has been stolen only when money disappears from the account — unless you rely on fraud prevention through data analysis. In the case of sites with SSL security features, such situations are almost impossible, since the browser uses a highly protected connection and takes advantage of the special SSL encryption method.
So the key question ("Is my site SSL secure?") will no longer bother or worry you. And the answer is obviously yes.
How does SSL work?
And now we’re ready to discuss how the secure socket layer works. We won't go into details (you hardly need them), just describe the general idea.
SSL protection is implemented through two main mechanisms: authentication and encryption. Scientifically, SSL Protocol uses asymmetric cryptography to authenticate exchange keys, symmetric encryption to preserve confidentiality, and message authentication codes to ensure message integrity.
It’s a bit complicated, right? Don’t worry, we’ll do our best to explain the whole scheme in simpler language. So, if the user fills in the contact forms on the site which uses an SSL security system, the browser turns the text into a random set of characters and sends the result to the server. Then a special program on the server side turns the encrypted message back into normal text.
To encrypt or decrypt a message, one needs a key. The easiest way is to change each letter in the word to the next one, as the example below illustrates:
![]()
Though, finding such a key is very easy. Of course, SSL encryption uses a much more complicated approach. Scammers will take years to sort through all the possible keys.
Interested? Well, let's talk about SSL security and how it works.
What is SSL encryption?
Okay, what type of encryption does SSL use? Actually, as we’ve already explained, 2 of them are involved in the operation of the secure sockets layer (SSL) certificate: symmetric and asymmetric.
-
Symmetric encryption means that one key encrypts and decrypts the message.
-
Asymmetric encryption requires two different keys, public and private ones. The public key encrypts the messages, and every browser sees it. A private key decrypts them and should be kept secretly on the server.
Symmetric encryption is more convenient, but the key must be known to both sides of the process. This is difficult to implement because there are many browsers, while the server where the SSL certificate is installed is only one. The server would have to send the key openly, which is clearly insecure. Therefore, asymmetric encryption is required in order to transmit a symmetric key.
Every time a visitor comes to the site, the browser generates a unique symmetric key, encrypts it with a public key, and sends it to the server. The server compares the private key with the public one and decrypts the message. The entire process takes a few seconds.
Types of SSL certificates
Certificates vary in degree of validation and in the number of domains. The SSL security features provided to users change accordingly either.
A degree of validation:
-
DV SSL - Domain Validation - a certificate with domain validation;
-
OV SSL - Organization Validation - a certificate with verification of the organization (company);
-
EV SSL - Extended Validation - a certificate with extended validation.
A number of domains:
-
Wildcard SSL - a certificate aimed at the domain and its subdomains;
-
Multi-Domain SSL (MDC SSL or SAN SSL (Subject Alternative Name)) - a certificate focused on multiple domains.
And now we'll describe the types of SSL certificates and conditions SSL providers ensure at greater length.
DV SSL (Domain Validation)
Such certificates are aimed at non-commercial sites since they only confirm the web server dealing with the resource. The DV certificate doesn't contain any identifying information in the organization name field. Usually, you can see "Persona Not Validated" or "Unknown" there.
The DV type is a relatively cheap SSL certificate available to individuals. To obtain it, you need to prove only the right to use a chosen domain name. The procedure is rather simple: the domain owner receives an email with a request to click the link to confirm the usage right.
As for the SSL cost, the prices for DV SSL as of January 2019 are as follows: $ 12-15 per year (according to ssl.com.ua).
The process of obtaining a DV SSL certificate takes only a few minutes.
A site protected by a DV certificate looks in standard browsers (in particular, Firefox) as follows:
![]()
The Google Chrome browser saves on a green color, so certificates look like the example below:
![]()
In the details of each certificate, you can see if it is a DV or OV type. In DV certificates, only the domain name is present.
OV SSL (Organization Validation)
OV SSL certificate is more reliable than DV since it additionally confirms the registration data of the company owning the online resource.
The certificate is intended for legal entities, and therefore the required by SSL information includes more details. To get OV SSL, you must prove the right to use a domain name and confirm company data. In addition, you should be ready to answer the control call of the certification authority to the phone number specified in the order form of an SSL certificate or available in public access (as a contact phone number of the company). It is also necessary to translate the registration documents into English and notarize them.
OV SSL certificate costs as of January 2019: from $ 65 per year and up depending on the activity category.
The process of obtaining a certificate takes about 3-10 days.
A site protected by an OV certificate looks in standard browsers (in particular, Firefox) as follows:
![]()
In the Google Chrome browser:
![]()
In OV certificates, there is information about the legal address and company name.
EV SSL (Extended Validation)
Now we’re talking about, perhaps, the best SSL certificate, the one considered the most reliable.
EV SSL first appeared in 2007. It is primarily aimed at websites conducting financial transactions and therefore needing the highest level of confidentiality. And EV SSL encryption technology is a great option because it provides web resources with maximum data protection.
These are so-called green line certificates available only to legal entities. And a company, which is ready to create an SSL certificate of such a type must be prepared to undergo a huge number of all sorts of checks - truly the seventh level of hell! The OV SSL requirements hold valid, but now they are supplemented with the check of a certificate of state registration and confirmation of being in the Unified State Register of Legal Entities.
EV certificates are useful if you need to tie up a domain with a physical organization. Here is an example of the Bank of America company and its domain bankofamerica.com. In this case, the certificate with the verification ensures that the resource in question really belongs to the actual bank (namely, Bank of America).
Moreover, EV certificates protect against “phishing sites” attacks, as was the case with the Mountain America Credit Union. The attackers managed to get a legal SSL certificate (but not of the EV type) for a copy of the quite reliable credit institution's website. The fact is that the bank (Mountain America Credit Union) used the domain name "macu.com", and the attackers chose "mountain-america.net", and their resource looked quite innocent. After receiving the certificate, the "innocent" SSL website was replaced with a phishing one. EV certificates seriously impede such a fraudulent maneuver. Well, at least, the address of the fraudster becomes immediately known.
DV SSL certificate cost (as of January 2019): $ 130-1300 per year.
The duration of the process of obtaining a DV SSL certificate is about 2 weeks.
A site protected by an EV certificate looks in standard browsers (in particular, Firefox) as follows:
![]()
In the Google Chrome browser:
![]()
As we’ve said earlier, a distinctive feature of EV certificates is a green line containing the company name displayed in the browser, which should indicate the maximum website SSL protection.
So we can safely summarize that the EV type ensures the most secure SSL certificates.
Wildcard SSL
Wildcard SSL is a certificate, which applies to the domain and the entire subset of its subdomains. Say, if the 'domain.ua' domain is used, the wildcard certificate will include the 'domain.com' domain itself, as well as any subdomains of the lower levels: mail.domain.ua, 1ev.domain.ua, r.info.dnipro.domain.ua, etc. Typically, such SSL certificates are visually designated as *.domain.ua and cost about 4 times more than DV does.
Multi-Domain SSL
Multi-Domain SSL is another example of SSL product: a certificate for several different domains. So a multi-domain SSL certificate can cover domain.ua, market.com, river.it domains, but it doesn't apply to subdomains.
How to get an SSL certificate?
We think, by this point, you've already matured a few questions, not the least of which is: "How do I get an SSL certificate for my website?". We're ready to answer it and describe the main details of such a tiresome procedure.
To purchase an SSL certificate, you should contact a special company called Certificate Authority (CA). The process can be implemented in 2 ways:
-
in automatic mode, through various scripts;
-
in manual mode, say, when receiving an EV certificate or filling out a form on the website of the SSL provider.
CA is a kind of administrative regulatory authority that issues SSL certificates to domain name holders. In addition, it is these organizations that conduct the appropriate checks when needed.
List of most popular CA:
-
Comodo
-
Symantec
-
GeoTrust
-
DigiCert
-
Verizon
-
GoDaddy
-
VeriSign (bought by Symantec)
-
GlobalSign
-
Let's Encrypt (issues free certificates)
Now you know how Secure Socket Layer works and where to order it... but what if you don't have the money to buy SSL? Is there a way out of such a situation?
Happily, yes, there is a way out.
A free way to generate an SSL certificate
If you cannot afford to purchase an SSL certificate, you have to consider a free option, the more especially as from 2014 onwards, there are services, which give you such an opportunity. At first, these were little-known Chinese SSL providers, then Let's Encrypt appeared, and now it is the monopolist of the market (as of 2019).
What's an SSL certificate from Let's Encrypt? What does it offer?
Its pros are obvious: Let's Encrypt is free of charge and ensures a fairly high level of services at the same time. Alas, there are also cons, such as:
-
certificate validity is only 90 days (but there are automatic renewal mechanisms). Just compare: the maximum validity of paid certificates is 27 months;
-
Let's Encrypt doesn’t issue OV and EV certificates.
But, technically, free DV certificates from Let's Encrypt are no worse than paid ones from other CAs and provide a similar level of protection.
You can get a certificate from Let's Encrypt using the command line and such clients as Certbot, acme.sh, etc.
The process of obtaining an SSL certificate
Now it’s high time we discussed how to install an SSL certificate, step by step.
The process of getting DV SSL certificates (no matter, free or paid) consists of the following steps:
-
The request formation. On the reseller's website of SSL certificates or a domain registrar resource (or in a terminal console), the user fills out a small form with basic information: domain, company and department names, email, etc. The result is the encrypted file, which contains all the data entered previously. It is called a CSR request (Certificate Signing Request).
-
Data confirmation. The CSR file is being sent to the CA. CA, in turn, checks in the DNS system the existence of an A record for the domain specified in the CSR. Also, CA asks the holder to confirm the right to use the domain in one of several possible ways. Among others, CA may require you to add a TXT record to your domain’s DNS system or a specific content file - to the hosting. Thus, CA will see that it is the domain holder who is trying to obtain a certificate, not somebody else.
-
Getting a certificate. If everything went well, it's time to generate an SSL certificate. That is, CA sends the certificate files to the email user (and we’re talking about a couple of documents, not a single file). In the classic case, the sent set contains the following files:
-
file with the .crt extension: public part, a signed certificate;
-
file with .key extension - private part, a certificate key (private key);
-
sometimes chain.crt files are also sent: intermediate certificate or certificate chain. But in most cases, the chain can be found in open sources.
-
Chain of trust
When a client's browser checks for a certificate on a site, it analyzes a few files called a chain of trust. The term refers to a sequence of several documents which certify each other: End-user Cert -> Intermediate Cert -> Root Cert
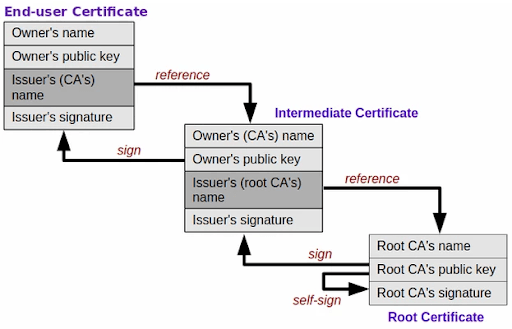
-
Root Cert is a certificate issued by a trusted CA. Root certificates are pre-installed in all web browsers and operating systems and considered to be unconditionally trusted, their reliability is beyond doubt.
-
Intermediate Cert is, as the name implies, an intermediate certificate signed by Root CA.
-
End-user Cert is, as you might have already guessed, an end-user certificate signed by a CA. This is the very SSL certificate to which our article is devoted.
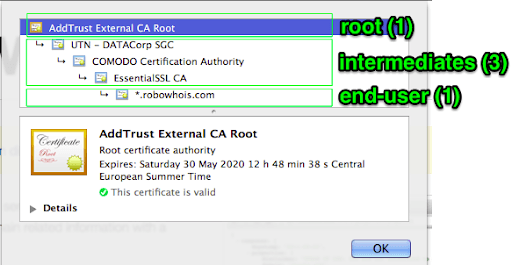
And now let’s see how the chain of trust looks in the browser (if you view the detailed information about the SSL certificate):
The check of your certificate
Now you may ask: “How do I check a security certificate for a site?”
The question is fair, and the answer is very simple. You can check your SSL certificate on a web server using the following public services:
-
SSLShopper offers a quick and simple way to check a chain of trust as well as the correctness of your certificate customization;
-
SSL Labs provides a detailed report on certificate and web server settings.
Summary
Okay, now you know how SSL works, what it really is, and how to check the website security certificate. So you have all the necessary information to protect your online resource properly.
Analyze the types of SSL certificates we've described earlier and choose the one that fully meets your requests. And if you need expert assistance, our team is always happy to provide it. And, of course, feel free to contact us with any questions regarding mobile and web development.