Today, many companies integrate their corporate processes with mobile platforms and have their own apps: it's convenient, profitable, helps to stay in touch with the consumer... However, we've talked about all this more than once. Now it's time to think about securing your applications and other digital communication channels. Otherwise, you risk making your business (as well as your clients) a victim of cyber crooks.
But what do you know about modern security standards and requirements for protecting business apps? If the answer is “next to nothing”, you should hunt down the issue at length and without delay. And, of course, we're prompt to come to the aid.
We’ll talk about top security trends in 2022, describe the overall market, and provide some useful tips on the subject. Put it differently, we’re going to initiate an interesting conversation to help you have an ear to the ground and meet the needs of your business safety.
So, let’s start our mobile security discussion!
Mobile security status 2022
In anticipation of the new year 2022, Trend Micro Incorporated conducted a cybersecurity risk study and shared the results with all of us. The report is entitled “The New Norm: Trend Micro Security Predictions for 2022”, and it states the following...
-
A growing number of threats when using DevOps and cloud systems. We perfectly understand the convenience of cloud storage, DevOps technologies, and the like: these solutions significantly increase business efficiency. However, they also put companies at risk of third parties. And in 2022, the situation, according to Trend Micro Mobile Security Predictions, will be even worse in this respect.
-
Active use of third-party software. Open-source libraries and APIs are a modern way to simplify the creation of mobile applications. As with cloud technology, it’s very convenient and efficient! However, experts predict that in 2022 the intensity of hacker attacks initiated due to the careless use of open-source tools will have increased significantly. So next year, companies should rethink their strategy related to analyzing and protecting against cyber threats.
-
Access to business data through code injection attacks. Increasingly, hackers will use SQL injection, deserialization errors, and cross-site scripting. And the main target will be third-party libraries or cloud service providers.
-
Remote workers as a threat to the corporate network. Next year, a relatively new type of risk will also appear, and its cause is remote employees as a potential threat to corporate information security. The reason is the low security of their Wi-Fi network. In addition, there are vulnerabilities in the connected home and mobile devices that can serve as an entry point to the corporate system.
From other sources, we’re also aware of other upcoming web, iOS, and Android security threats that should be feared in 2022:
-
The need to provide information security when introducing new technologies (such as AI, big data, cloud & mobile solutions, robotics). In 2022, the active transition to the digital economy will continue, which entails various cyber risks. To avoid them, you need to think about mobile app protection and information security tools beforehand. Moreover, it’s advisable to solve IS issues proactively, at the very start.
-
The growing role of the state in the information security market. Next year, the need for investing in Mobile Threat Defense is going to be caused not only by an increasing number of cyber risks but also by new requirements on the part of regulators. States of different countries toughen up IS requirements, especially when it comes to financial institutions.
-
Compositional change of active users of web and mobile security solutions. Previously, mainly representatives of the financial sector were engaged in information security technologies. Recently, however, companies from other industries have also begun to actively invest in these projects.
Top Mobile Security Trends
Now is the time to discuss the latest security trends: what should businesses somehow related to mobile (or any information) technologies expect in 2022?
Adaptive mobile security
Adaptive security means an integrated approach to responding to mobile threats.
This kind of strategy considers risk management and information security as an ongoing process based on predicting and preventing cyber threats. In addition, it’s about always staying on guard, being alert, and ready for new mobile app vulnerabilities.
Protecting sensitive public data
Business digitalization has led to a growth in the volume of corporate, financial, and personal data stored in cloud systems. Alas, in 2022, significant information leaks are expected, which means the issue of sensitive data protection is the most acute trend in mobile security.
Among the ways to protect databases, the technology of masking and encrypting information can be noted. But this is not enough! Data theft is a cash cow of cyber-criminals, and therefore they come up with new ways to break into cloud systems.
The main objectives of mobile security attacks, including database hacks, are:
-
illegal receipt of funds;
-
hidden mining;
-
various extortions;
-
data theft for resale;
-
industrial espionage.
The number of databases in the infrastructure of companies is constantly growing, one organization may have several of them, each focused on its own specific business task. And all these databases require protection, often complex and costly.
A good solution is to consolidate multiple databases on a single server. Such a strategy allows simplifying the management approach and using equipment resources as efficiently as possible.
Providing the best phishing protection
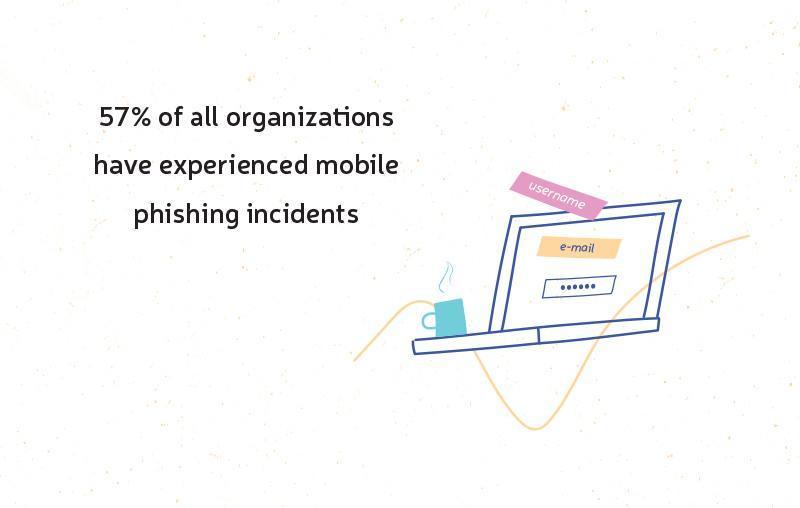
Phishing attacks remain one of the most dangerous cyber threats. Their key purpose, as you’re probably aware of, is to gain access to confidential user data: logins and passwords, credit card numbers, email, etc.
According to a new study, over the past year the number of phishing cases has increased: every 15-20 seconds, another fraudulent resource appears. And in 2022, such a sad tendency won’t stop growing.
So how can a phishing attack differ in 2022? Let’s see!
-
Phishing outside email. Phishing attacks via email and other similar channels are nothing new, and companies are taking necessary measures to provide proper protection. However, now is the time for a phishing attack through the mobile environment. And not all businesses are ready to respond to a new threat from hackers.
-
SIM Jacking or activating a phone number on the criminal’s SIM card. The process is simple: the fraudster contacts the representatives of the mobile operator of a particular client and convinces them that the SIM card is hacked, so it's necessary to transfer the phone number to another card. If such an operation is successful, the cybercriminal gains access to the entire digital life of his victim, including email, social networks, and mobile app accounts.
-
Using real information events to start phishing attacks. An example is the 2022 Summer Olympics in Tokyo (or something else of the sort). An attacker creates a fake ticket sales application and takes similar criminal actions: say, he sends out allegedly promotion mailings with malicious links. Unfortunately, even the best mobile security measures aren't always able to prevent the harmful consequences, it's important that the user himself also be vigilant.
-
Phishing attacks using well-known brands. Lately, scammers have been hiding behind the name of a certain famous company in order to achieve their goal. It's a smart step: agree, such names as Google, Facebook, or Apple, inspire trust in users who don't mind receiving SMS mailing from these renowned brands. And in 2022 there will be more cases of the sort.
-
Using encryption techniques by scammers. Cybercriminals are inventing new ways to implement phishing attacks, among other things, they resort to encryption and HTTPS verification-based sites.
Fighting the growing impact of mobile malware
Mobile malware is also becoming an urgent problem, which means protecting applications from its influence is one of the top security trends in 2022.
By the by, according to Counterpoint Technology Market Research, in 2022, cyber crooks will use remote access protocols to spread malware. In addition, some hackers plan to create and actively promote malware packages to allow other fraudsters, not versed in programming and not having relevant experience, to get ready-made products for their criminal actions.
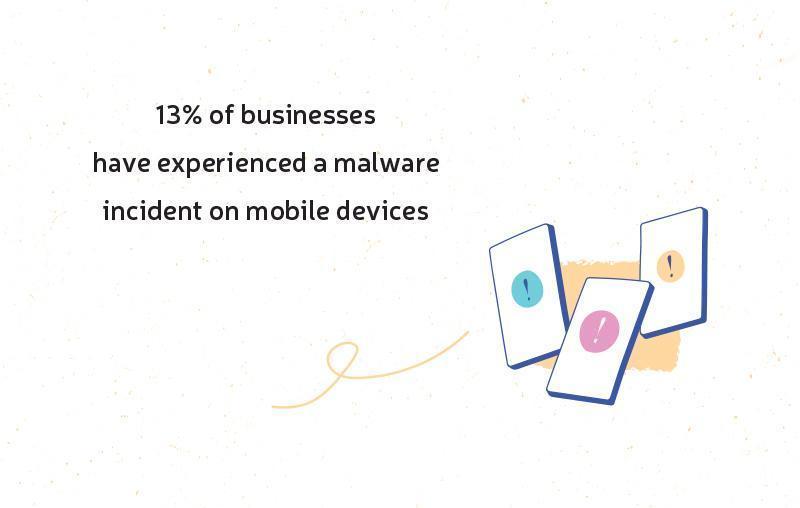
Malware comes in different types: adware programs, spyware, viruses on Android devices and iOS ones, ransomware, and so on.
A little confused here? Okay, let's take a look at the problem step by step:
-
Theft of private data. Most often, malware is designed to steal confidential information for financial use.
-
Blocking access to valuable data. Now we’re talking about ransomware. Imagine: your access to certain important files or data is blocked, and the fraudster promises to rectify the situation when his requirements (usually financial) are met.
-
The inconvenience of using applications. A good example is adware programs: they aren’t really dangerous, but they keep annoying users. In addition, sometimes adware contains precarious links.
Since 2018/19, the IS experts have been trying to solve the problem of malware by introducing protection at the hardware level. And developers are going to continue working on this area in 2022. Such an approach is aimed at preventing software forgery, as well as providing secure authentication and authorization.
Our list of mobile app security trends includes another item closely related to the one we’ve just discussed, namely…
Mobile Device Management
Today, many companies are actively using mobile devices to organize their business processes. So, the requirements for mobile app protection have grown appreciably. That’s why great attention is paid to Mobile Device Management.
Among other things, the solution in question allows you to:
-
safely integrate employee’s mobile devices into the corporate environment;
-
create a securely encrypted container with confidential information on each employee’s device;
-
apply corporate security policies to users ’devices (say, an employee cannot take advantage of a certain corporate service if his device isn’t password protected).
SoC approach
Given current market conditions, the task of detecting and correctly responding to cyber-attacks comes to the fore. Therefore, in 2022, mobile security trends associated with the SoC creation will gain popularity.
SoC means the Security Operation Center and includes three main components:
-
the improvement and adaptation of protection technologies;
-
hiring employees whose primary responsibility is information security;
-
the formation of modern security standards and rules that allow building clear processes aimed at preventing cyber threats, as well as the correct response to them.
MSSP (Managed Security Service Provider)
Next year, according to forecasts, more and more large and medium-sized companies are going to resort to the help of MSSP - Managed Security Service Providers. Their role is clear from the name itself: they provide commercial information security services.
Benefits of MSSP:
-
cost reduction due to the lack of the need to buy specialized software (cooperation with MSSP is cheaper in the end);
-
a higher level of information protection and more reliable web & mobile security solutions as services are being provided by experienced professionals;
-
the opportunity to fully focus on the core business without thinking about digital security all the time.
But it should be remembered that, according to the report mentioned in the first section of our trend security review, in 2022, attackers will also use Managed Service Providers as a channel for compromising businesses. In this way, cybercrooks would be able to steal valuable corporate data and install malware quite easily.
So, figuratively speaking, MSSP is a double-edged sword.
Biometric User Identification
Biometric identification is a good way of protection, and it has been used for a relatively long time. Just think of Apple’s Face ID and Touch ID! It’s a good example, right?
However, the issue will greatly progress in 2022. The reason is the formation of a universal biometric system, which many countries insist on and even offer a special legislative framework.
Such a system implies biometric identification of citizens, that is, the creation of a single database of all biometric data. It may simplify the interaction between users and financial institutions by accelerating the processing of various kinds of transactions (since the user's identity determination won't require the passport anymore, it'll be enough to compare the voice and face of the client with the entries in the database).
On the other hand, this sort of identification is considered quite reliable (on the stipulation that the financial company is able to provide secure reception, storage, and transfer of biometric data of its customers).
Identity Management (IDM)
Of course, the best mobile security requires reliable multi-factor authentication and intelligent device identification, especially when it comes to business systems. It perfectly explains the emergence and development of IDM services, which use a new identification approach.
The plain truth is that by now, the authentication model is no longer user-centric. Today it's based on a machine component. And Identity Management systems are taking full advantage of it.
Therefore, companies are actively introducing IDM systems to be able to:
-
simplify the process of managing business systems, which are often tied to mobile devices;
-
automate the provision of access to users based on company policies;
-
eliminate the factor of human error;
-
withdraw unnecessary access from a user whose role in the company has changed (say, if he was fired or changed his position).
Machine Learning as applied to mobile app security
Machine learning-based protection is already in use among many security vendors. And in 2022, the trend is expected to be still relevant, allowing businesses to build more flexible and adaptive threat detection techniques.
Machine learning-based protection aims to:
-
monitor activity to detect malware;
-
process and analyze data efficiently;
-
predict probable threats and cyber attacks.
Alas, there is a dark side to all this either. Unfortunately, not only do mobile security providers use machine learning solutions; hackers, too, managed to find a way to benefit from them.
Most cyber-attackers adopt machine learning techniques to create phishing systems, develop malware that bypasses signature methods of detecting, and search for vulnerabilities in application code. The next step, experts say, is likely to be the use of machine learning tools to study business software to detect the least secure systems and mobile app vulnerabilities.
So companies must be ready to take up such a challenge.
Collaboration among cybersecurity solution developers
Developers often collaborate, creating open-source libraries and sharing their own experiences and best practices. The matter also applies to mobile app security.
In 2022, the cybersecurity software development community might expand even further. The mobile app security Q&A area is also likely to become more active: experts have already been helping each other by answering questions on the topic (a vivid example is Quora), and such a trend will keep evolving.
Information Security Awareness
Our discussion of top mobile security trends concludes with a very important item on the list. It's about raising awareness of users, chiefly - employees of large companies.
The fact is that sometimes a person himself, voluntarily, gives all the necessary information to cyber-spies. And if such a person works in a renowned corporation, the consequences can be terrible.
To avoid such an outcome, the company must constantly raise the awareness of its employees by telling them about popular mobile security attacks and ways to prevent them.
Effective employee training involves:
-
distance learning;
-
the ability to view materials on different devices at any time;
-
personalization of materials for a specific audience;
-
micro-learning (which means providing training information in small blocks);
-
gamification (rewards and achievements, the use of fascinating stories and characters, etc).
Summary
Our conversation is now closing down, and in the end, we'd like to give some tips on countering mobile threats.
So, it’d be smart of you to take the following steps:
-
checking the reliability of cloud service providers and MSSPs;
-
assessment of vulnerability and risks of third-party solutions;
-
investments in digital security tools;
-
revision of security policy regarding remote workers.



