When securing your organization, don't forget to protect mobile applications your company owns and makes money on either. It’s really important, since phishing attacks, data leakage, poor user authorization, and other vulnerabilities would harm your customers, which means these cyberthreats negatively affect your business reputation.
If you want to know more, as well as learn what steps to take to keep mobile apps safe, read our article.
What is mobile app security?
The app popularity surprises no one anymore, these services have proliferated in the market: as statistics claims, in 2018 mobile services had been downloaded more than 200 billion times. And this is hardly their limit.
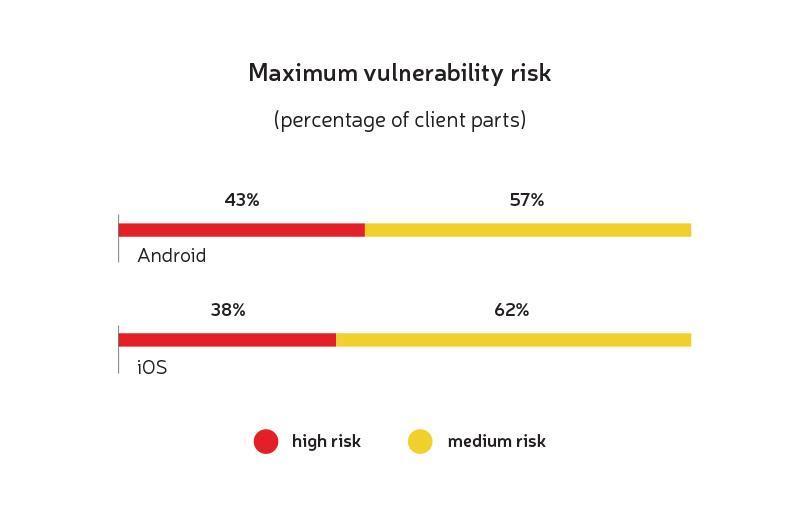
Alas, other statistics are less encouraging: high-risk vulnerabilities were found in almost 40% of applications (for each operating system). To be precise, 38% of vulnerabilities are related to iOS programs, and 43% concern Android apps.
What causes mobile app vulnerabilities?
The main causes of software protection problems will be described below: in detail, with all the necessary explanations. In the meantime, let's just say it’s usually about the wrong approach to mobile security.
And what's more, a vast number of vulnerabilities are being formed at the development phase, although they might become apparent much later: at the moment when their elimination requires significant code rewriting. So it's better to protect the app code at the initial stage. This will save you from unnecessary work and extra costs in the future.
And remember: sometimes a few minor protection breaches, when combined, get a synergistic effect, which leads to disastrous consequences. Though individually each of these breaches doesn't greatly affect the mobile app security.
Why care about protection against mobile malware?
You must take care of your mobile apps' security, for your business application directly influences your company's reputation. Why is it so? Let's take a look.
Imagine: you’ve chosen the wrong mobile security strategy, and as a result, your customer data was stolen and misused by cyber scams. Sooner or later, your clients are going to find out what exactly happened, and their trust in you and your company will decrease significantly. And you don't want such an outcome, do you?
The pitiest stories are when data related to financial transactions are stolen. In this case, unreliable app protection might cost a user his money, which he is unlikely to be happy with. And it is you, your company, who will be to blame for these monetary losses. At least, the deceived user, he is also your client, would think so.
By the by, major market players also face such problems. A striking example is Air Canada, whose application was hacked in the late summer of 2018. Sad thing is that it all happened due to a really small gap in mobile protection. But, small or not, the upshot was unfortunate: attackers had stolen the personal data of 20,000 users.
Air Canada representatives had to temporarily block clients’ accounts and ask users to come up with new login-password combinations (of course, after the security error had been fixed).
Surely, Air Canada clients weren't thrilled with such news, and their loyalty decreased to some extent. The company was forced to take certain measures to re-earn the lost reputation points.
And this is just one example of why business owners must build security into their apps.
Top mobile app security vulnerabilities
Before discussing the proper approach to mobile security, let's consider the main app vulnerabilities.
Poor authentication & authorization
Work with a new application starts with user authentication and authorization - procedures intended to protect personal, sometimes strictly confidential data.
By the way, what is the difference between these concepts?
-
Authentication is designed to confirm the identity of a particular user and based on verification of his accounting data. In case of incorrect input of verification information (say, a password or PIN), the application should be blocked.
-
Authorization occurs after confirming the identity of the user, the task is to find out which services he has access to. For example, in a large corporation, senior managers may have access to more system features than regular employees.
As you understand, authorization and authentication should be approached very responsibly. Don't consider that any authenticated user may gain access to full functionality. When it comes to securing your organization, you can't be too careful, can you?
And one more tip: don't forget to repeat the authentication process from time to time to make sure you're still dealing with a registered user, and not a cyber cracker.
Weak server-side controls
Mobile applications are mostly based on client-server architecture. The program downloaded to the smartphone from App Store or Google Play is the client part, which some users consider the main and even the only one. In the end, they work with the client part all the time: make purchases, view messages, and more. However, we shouldn't forget about the server component, which is on the developer's side and interacts with the mobile client via the Internet, usually through a special interface (API). It is the server part that is responsible for the correct execution of app functions.
A few years ago, server vulnerabilities were the most damaging to mobile app security. Say, in 2012, Weak Server Side Controls ranked second in OWASP Mobile Top 10. However, in 2016 the situation changed, and server-side problems ceased to be such a dangerous threat.
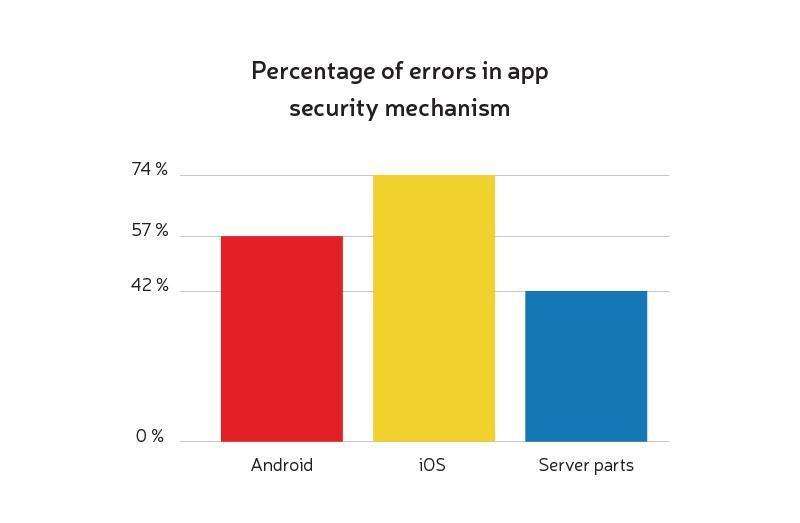
Alas, despite these favorable changes, server-side vulnerabilities still exist. Studies show that more than 40% of server components have an unsatisfactory level of security, while almost 35% contain extremely dangerous vulnerabilities.
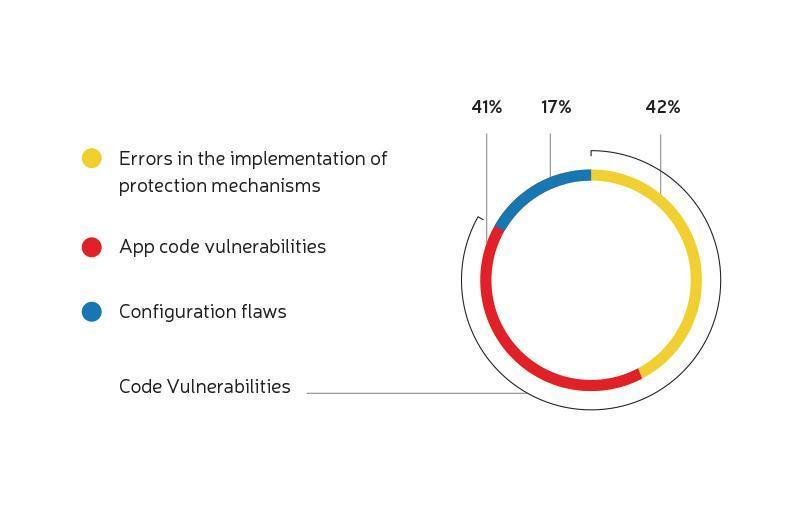
As the above infographic illustrates, for each configuration problem, there are about 5 code vulnerabilities (which also include errors with the protection mechanisms).
Client-side injection
Now let's talk about the client-side injection.
According to statistics, today more than 60% of vulnerabilities are located in the client part. Moreover, a third of the problems of this kind have a fairly high level of risk.
Vulnerabilities in the client are diverse, such as…
Authentication problems
About 40% of all applications authenticate the user on the client-side, which implies its storage on the smartphone. The described approach to mobile security, of course, is unsafe: identification data is stored incorrectly in more than half of the apps. It would be smarter to perform server-side verification by transmitting authentication data as hash values.
Infected software
According to McAfee, infected software appears with increasing frequency: by the end of 2018, the number of malware had amounted to almost 30 million, which led to the growth and intensification of attacks on client apps.
And bear in mind, even a new device may be unsafe. Examples include Alcatel smartphones, initially infected with spyware. As a result, unsuspecting users continued to buy Alcatel products for quite some time.
And one more thing to remember: a cyber crook doesn’t always need physical access to the device in order to steal user data or commit another unseemly act.
The conclusion is simple: you must take care of quality protection against mobile malware from the very beginning.
Incorrect data storage & encryption
Now it's time to talk about the most serious app vulnerability, namely, unreliable data storage. After all, it is data theft that leads to many unsuccessful outcomes, sometimes of a financial nature.
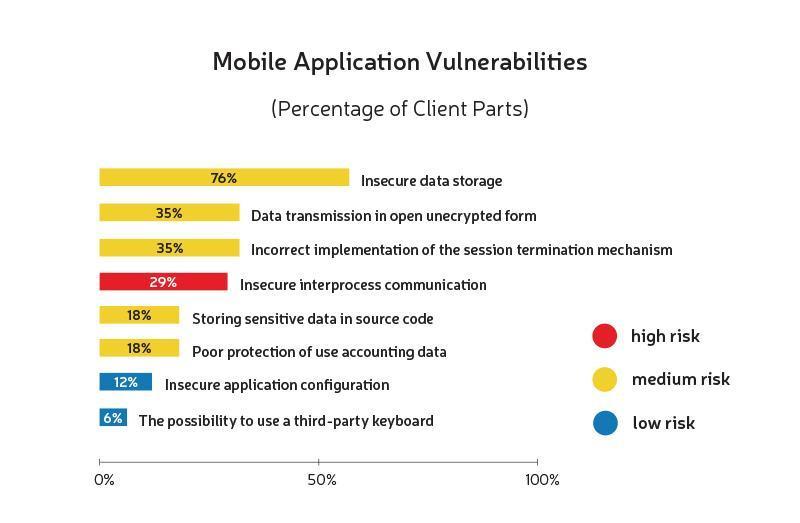
Let’s start with another piece of sad statistics: not less than 75% of applications cannot boast of secure information storage. And the issue concerns even confidential financial data, which is especially dangerous.
A good solution to the problem of secure storage and transmission of information is its encryption. It means encoding the data before sending it and decoding it on the receiving device.
Surely, information encryption is a great way to protect mobile applications but you have to understand that not all encoding and decoding methods are equally effective. If the developer is poorly versed in data encryption algorithms, a cyber attacker would be able to intercept the user's personal data without much trouble.
Unintended data leakage
Developers often forget about this problem and get focused on other types of information protection, not directly related to possible data leakage while using a mobile app.
We give an example. Let's say there is an application with a session identifier in the link to the file the program is processing. And now imagine a scammer who managed to convince a user to send him the link in question, which he did, not suspecting that he would also send a data identifier with it... thus, the attacker gets the opportunity to act on behalf of this user. And if the developer had taken care of proper data protection against information leakage in advance, this would never have happened.
But the problem can occur not only through the developer’s fault. Much depends on how vigilant and careful the user himself is, for information leakage can result from unsafely downloaded programs or incautious granting someone elevated privileges (or something else of the sort). And since it is the user who will suffer due to data leakage, it’d be wise of him to consider making mobile security his priority.
Third-party libraries (APIs)
Third-party API services and libraries are of great help in mobile app development. They save our time and effort by allowing us to take advantage of ready-made pieces of code in order to implement a specific solution: a payment gateway, video streaming, a cryptocurrency wallet, and so on.
The modern market is full of various APIs: some of them are paid, some are free to use. There are plenty to choose from. However, not all of the provided third-party services have a high level of protection, which is why user data can be severely damaged.
Lack of binary protections
Binary protection is something that cannot be ignored. Neglecting such a measure would lead to your application becoming easy prey for a cyber attacker: he'll have no trouble analyzing and using it to his advantage: say, he may rewrite the code a little bit and resell it as an allegedly new mobile program (which is equal to stealing).
Binary protection prevents this by complicating the whole process.
The best mobile security strategy
We've already covered some of the tips regarding making mobile security when describing application vulnerabilities and types of phishing attacks. Let's systematize all of the above and provide a few more useful recommendations to help you keep mobile apps safe.
-
Transfer part of the app to the server. Transferring part of the program logic and algorithms to the server can help protect mobile applications. If the server is correctly configured and reliably secured, cracking it would be a tricky task.
-
Keep the security of your code. Unfortunately, a fraudster would be able to get access to your code through the public version of the mobile program. So, first of all, make sure he’ll get nothing out of it. To achieve the goal, you need to protect the app code as best as possible. Let it be concise and strong, based on the most modern algorithms. Also, ensure it’s being carefully tested: not once, but on a regular basis. Keep in mind, even the smallest code errors and bugs might lead to app cracking.
-
Think of user code protection. Any user code must have a strictly limited number of input attempts, after which, in case of failure, the application should automatically log out or even be blocked.
-
Use innovative encryption techniques. We've talked over the matter of the importance of data encryption. Therefore, you know why you should store and process sensitive user data in encoded form. Also, it'd be smart of you to consult with mobile app security experts to find out if the encryption algorithms you're using are quite effective.
-
Take care of the correct authentication. To reliably protect user accounting data, you need to provide multi-factor authentication: a multi-step verification process based on several levels of security. This may include checking the username and password, sending SMS with a secret code, and more of the sort. Such precautions are especially important for financial and law enforcement organizations.
-
Use API keys responsibly. API keys are known to be used to authenticate user connections. If this is your case, make sure you don’t store them publicly, in free access.
-
Be careful with third-party libraries:
-
Don't trust open-source services and tools implicitly. The exception is time-tested solutions that have long and successfully been used by large companies. An example is the Realm database, which takes advantage of built-in encryption.
-
On the other hand, resorting to the help of closed-source libraries is also unreasonable. It’s really unwise, for you won't have the possibility to assess the quality of the code and the effectiveness of the chosen mobile security strategy.
-
-
Apply hack detection technology. We’re talking about algorithms allowing you to configure the notification system in case of attempts to crack the code. In addition, you can protect app code by making it stop working if it’s been illegally changed.
-
Don’t ignore simple precautions. The program shouldn’t be allowed to display confidential user data on the smartphone screen brightly, in large type. The advice may seem too simple, but it's also important.
-
Ongoing updating and testing of the application. If you think you may create an application and let it be as it is, then you're wrong. Every year there are more ways of cyberattacks appearing, and you have to be ready to meet these new challenges. Therefore, continuous updating, backed by testing, is your only choice.
Summary
Now you understand why you need to budget for mobile apps’ security. This isn’t an extra expense, as it might seem at first glance; here we’re talking about a contribution to future prosperity and the prevention of possible financial and reputational losses.
That’s why our experts take protection against mobile malware and other vulnerabilities very seriously. The apps and websites we create are secured at a high level.


